Advanced Endpoint Detection & Response with Deep Inspection
TreeIQ™ Protect EDR delivers advanced detection, deep behavioral inspection, and response capabilities designed to stop sophisticated attacks that bypass traditional security controls. It provides continuous endpoint visibility, layered execution controls, and configurable protection levels to match different risk environments.
Adaptive EDR Protection Levels
TreeIQ™ Protect EDR operates in three configurable enforcement levels, allowing organizations to balance security and usability:

Low
Monitoring and detection-focused enforcement

Medium
Balanced prevention with controlled execution restrictions

High
Maximum security with aggressive attack surface reduction
Policies can be applied per group or endpoint.
Deep Inspection Engines
TreeIQ™ Protect EDR uses multiple deep-analysis engines to detect advanced threats and malicious behavior:

DeepLookIQ Inspection
Deep behavioral inspection of processes and runtime activity

DeepExploitIQ Inspection
Detection of exploit techniques and exploit chains

DeepDiveIQ Inspection
Deep system-level behavioral correlation

DeepScriptIQ Inspection
Script-based attack and abuse detection

DeepDive Level 2
Advanced second-level inspection for high-confidence threat validation
Advanced Execution Control & Attack Surface Reduction
TreeIQ™ Protect EDR actively blocks common attacker techniques by restricting risky execution paths.
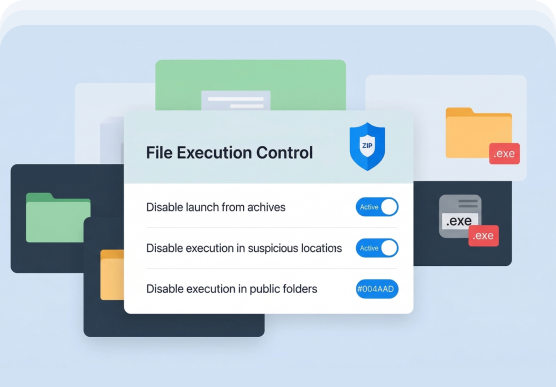
Archive & File Execution Control
- Disable launch of executables from archives
- Disable execution in suspicious locations
- Disable execution in public folders
Partner & OEM Engagement
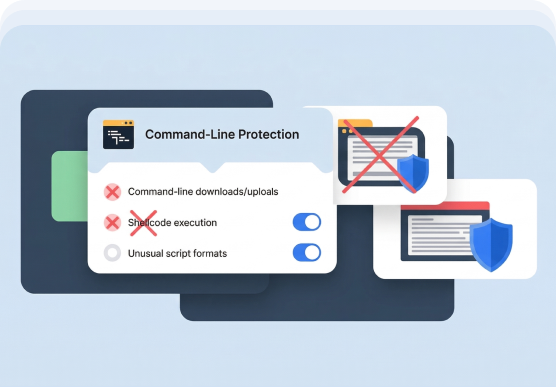
- Disable command-line downloads and uploads
- Disable shellcode execution via command-line
- Disable unusual and uncommon script formats
- Disable execution from script processors
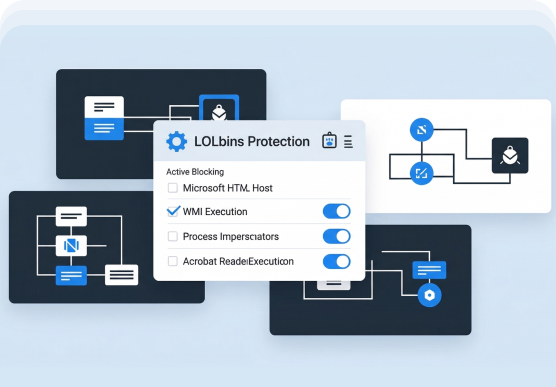
Living-off-the-Land (LOLbins) Protection
- Disable execution from Microsoft HTML Host
- Disable execution via Windows Management Instrumentation (WMI)
- Disable Windows process impersonators
- Disable execution from Acrobat Reader
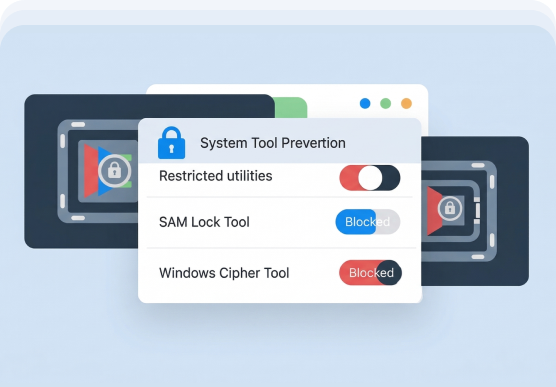
System & Tool Abuse Prevention
- Disable use of SAM Lock Tool
- Disable use of Windows Cipher Tool
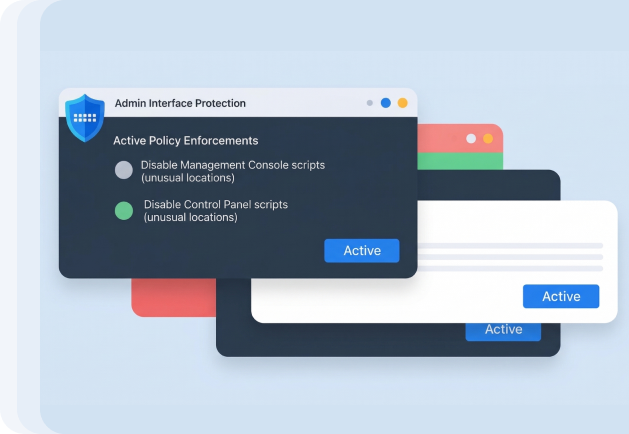
Administrative Interface Abuse Protection
- Disable Management Console scripts from unusual locations
- Disable Control Panel scripts from unusual locations

Core Protection
- Behavioral malware and zero-day threat detection
- In-memory and fileless attack protection
- Behavioral ransomware detection and automatic blocking
- Zero-day exploit technique prevention
- Advanced behavioral blocking (HIPS)
- Lightweight antivirus and antimalware engine with low system impact
- Network-level attack, botnet, and C2 communication defense
- Phishing and malicious domain protection
- USB device protection and control

Centralized Web Admin Console
- Web-based centralized management console
- Easy creation and management of endpoint groups and clients
- Single dashboard for endpoint status, actions, and events
- Centralized policy creation and deployment across multiple groups
- Easier control of security policies and workstation settings
- Endpoint asset details and inventory visibility
- Single console to manage endpoint security and web security
- Designed for managing large and distributed enterprise networks

Policy & Access Control
- Different security policies for onsite and offsite users
- Policy enforcement at group and individual endpoint level
- Role-based administration (RBAC)
- Easy creation of sub-admins with delegated permissions
- Secure sharing of administrative responsibilities

Deployment & Usability
- Easy-to-use installation wizard with zero configuration
- Faster deployment of customized settings per group or per endpoint
- Intuitive and user-friendly admin interface
- Scalable deployment across large endpoint environments

Real-Time Threat Hunting & Analysis
- Real-time threat hunting across endpoints
- Proactive identification of suspicious activity
- Threat investigation with historical visibility

Threatvault & Sandbox
- ThreatVault centralized repository of detected threats
- Historical threat analysis and tracking
- Sandbox for isolated analysis of suspicious and unknown files
- Deep inspection for advanced and zero-day threats

Logging, Monitoring & Reporting
- Scan log
- USB device and event logs
- Threat history and security event tracking
- ThreatVault logs
- Blocked web access logs
- Threat history and security event tracking
- Predefined system reports
- Customizable reports for audit and compliance needs

Network Control & Trust Management
- Network whitelisting for trusted IPs, domains, and services
- Better governance of enterprise network communication
- Reduced false positives with flexible trust controls
Ideal For
Small offices and growing teams that need reliable endpoint security without backup or advanced data protection features.

· Organizations requiring advanced endpoint detection & response

· Enterprises facing fileless, script-based, and exploit-driven attacks

· Security teams needing greater control over endpoint execution behavior
Why TreeIQ Protect EDR?
Deep behavioral inspection beyond signature-based detection
Configurable enforcement levels (Low / Medium / High)
Strong prevention against fileless, script-based, and
Built-in attack surface reduction controls
Designed for modern threats and advanced adversary techniques
System Requirements

Supported OS
· Windows 11, 10, 8.1, 8, 7, Vista & XP (32-bit and 64-bit)
Processor
500 MHz or faster

Memory (RAM)
2 GB minimum

Disk Space
256 MB free space

Web Console Browsers
Internet Explorer, Chrome, Edge, Firefox, Opera, Safari (Latest updates recommended)
TreeIQ™ Protect EDR – FAQ
What is TreeIQ™ Protect EDR?
TreeIQ™ Protect EDR is an advanced Endpoint Detection and Response solution that provides continuous endpoint visibility, behavioral detection, and response capabilities to identify and contain advanced cyber threats.
How is TreeIQ™ Protect EDR different from traditional antivirus?
Traditional antivirus relies mainly on signatures. TreeIQ™ Protect EDR detects unknown, fileless, and zero-day attacks using behavioral inspection and real-time threat analysis.
Does TreeIQ™ Protect EDR protect against ransomware?
Yes. TreeIQ™ Protect EDR includes behavior-driven ransomware detection and blocking to stop malicious encryption activity early.
Can TreeIQ™ Protect EDR detect fileless and in-memory attacks?
Yes. It detects in-memory malware, reflective injection, and script-based attacks that bypass disk-based defenses.
What response actions are supported?
Response actions include terminating malicious processes, blocking execution paths, and escalating policies based on threat severity.
Does TreeIQ™ Protect EDR support threat hunting?
Yes. It supports real-time and historical threat hunting across endpoints.
Is TreeIQ™ Protect EDR suitable for enterprises?
Yes. It is designed for large and distributed enterprise environments.
How is TreeIQ™ Protect EDR managed?
It is managed through a centralized Web Admin Console for visibility, investigation, and policy control.
Can TreeIQ™ Protect EDR work with other security tools?
Yes. It can complement existing enterprise security tools.
Does TreeIQ™ Protect EDR require constant cloud connectivity?
No. It does not require mandatory public cloud dependency.
Is TreeIQ™ Protect EDR suitable for SOC teams?
Yes. It supports SOC operations, incident response, and investigations.
What threats does TreeIQ™ Protect EDR focus on?
It focuses on ransomware, fileless attacks, exploit techniques, and living-off-the-land attacks.
Does TreeIQ™ Protect EDR impact performance?
No. It is designed with a lightweight architecture for minimal system impact.
Can policies be customized?
Yes. Policies can be customized per group or endpoint.
Is TreeIQ™ Protect EDR part of the TreeIQ™ platform?
Yes. It integrates with other TreeIQ™ security solutions.
