Actionable, High-Fidelity Threat Data for Proactive Security
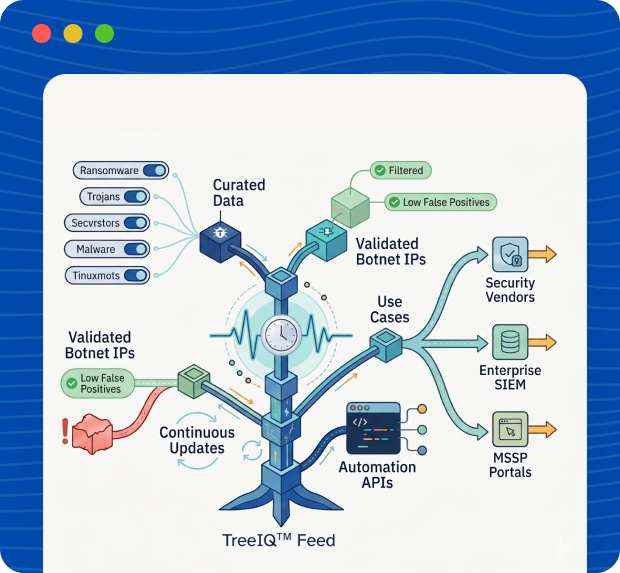
TreeIQ™ Threat Intelligence Feeds deliver continuously updated, high-confidence threat data that helps organizations, SOC teams, MSSPs, and security platforms detect, block, and respond to threats faster.
Built from real-world detections and deep analysis, TreeIQ™ feeds are designed for direct consumption by security products, SIEMs, firewalls, EDR/XDR platforms, and custom security systems.
What Are TreeIQ™ Threat Intelligence Feeds?
TreeIQ™ Threat Intelligence Feeds provide machine-consumable indicators of compromise (IOCs) that enable proactive defense against malware, phishing, command-and-control infrastructure, and emerging threats.
The feeds are available in raw, structured formats suitable for automation and large-scale ingestion.

Malware Feeds
Raw Processed Threat Feeds with Categorization
TreeIQ™ Raw Processed Malware Feeds provide pre-processed, enriched threat intelligence instead of simple raw dumps. Each indicator is classified, validated, and tagged to make it immediately usable across security platforms.
Unlike basic hash lists, TreeIQ™ raw feeds are processed intelligence feeds that include threat context and categorization, enabling faster and more accurate security decisions.

Includes:
- Malicious file hashes (MD5 / SHA1 / SHA256)
- Processed and validated malware indicators
- Threat category classification (e.g. ransomware, trojan, spyware, downloader)
- Malware family and risk context (where applicable)
- Clean, structured feed format for automation
Threat Categories Covered:
- Ransomware
- Banking & credential-stealing malware
- Trojans & backdoors
- Downloaders & droppers
- Spyware & surveillance malware
- Cryptominers
- Botnet-related malware
Use Cases:
- File reputation and malware blocking
- SIEM / SOAR correlation with threat context
- Threat hunting with categorized indicators
- Security product enrichment (AV, EDR, XDR)
URL Feeds
Malicious & High-Risk URL Intelligence
TreeIQ™ URL Feeds identify malicious and suspicious URLs associated with phishing, malware delivery, scams, and exploit hosting.
Includes:
- Phishing URLs
- Malware download links
- Exploit and dropper URLs
- Suspicious and high-risk web destinations
Use Cases:
- Web gateway and firewall blocking
- DNS filtering
- Email security integration
- Phishing prevention

Android Malware Feeds
Mobile Threat Intelligence
TreeIQ™ Android Malware Feeds provide intelligence on malicious Android applications and mobile threats targeting users and enterprises.
Includes:
- Malicious Android app hashes
- Trojanized and repackaged apps
- Spyware, banking trojans, and ransomware
- Command-and-control indicators
Use Cases:
- Mobile security platforms
- MDM and enterprise mobility solutions
- App reputation and risk scoring
- Threat research and mobile SOC operations

Feed Delivery & Integration
TreeIQ™ Threat Intelligence Feeds are designed for easy integration and automation.

API-based access

Periodic feed updates (real-time / scheduled)

Raw and structured formats

Easy ingestion into SIEM, SOAR, firewalls, EDR/XDR, and custom platforms
Why Choose TreeIQ™ Threat Intelligence Feeds?
- High-confidence, curated threat data
- Low false positives
- Continuous updates
- Ready for automation and large-scale use
- Suitable for security vendors, enterprises, and service providers
Who Should Use TreeIQ™ Threat Intelligence Feeds?

Security Operations Centers (SOC)

MSSPs & MDR providers

Security product vendors

Enterprises with in-house security teams

Threat research and intelligence teams
TreeIQ™ Threat Intelligence Feeds – FAQ
What are TreeIQ™ Threat Intelligence Feeds?
TreeIQ™ Threat Intelligence Feeds provide processed, categorized, and continuously updated threat data to help organizations proactively detect, block, and respond to cyber threats.
How are TreeIQ™ Threat Feeds different from raw threat lists?
TreeIQ™ delivers validated and categorized intelligence with context, reducing false positives and enabling faster automated enforcement.
What types of Threat Feeds does TreeIQ provide?
Malware Feeds, URL Categorization Feeds, and Threat IP Feeds.
What threat categories are included?
Ransomware, banking trojans, spyware, phishing, botnets, exploit infrastructure, brute-force and DDoS sources.
How frequently are the feeds updated?
Feeds are continuously updated and available via API, scheduled updates, or bulk downloads.
How can TreeIQ™ Threat Feeds be integrated?
They integrate with firewalls, web gateways, DNS filters, SIEM, SOAR, EDR/XDR, NDR, and custom platforms.
Are the feeds available via API?
Yes. TreeIQ™ provides high-performance APIs for real-time and bulk queries.
Can Threat Feeds be used in offline or on-premise environments?
Yes. Offline and on-premise database deployments are supported.
Who should use TreeIQ™ Threat Intelligence Feeds?
SOC teams, MSSPs, MDR providers, security vendors, enterprises, and OEM partners.
Do TreeIQ ™Threat Feeds generate false positives?
TreeIQ™ focuses on high-confidence intelligence, significantly reducing false positives.
Can TreeIQ™ Threat Feeds be customized?
TreeIQ Threat Intelligence Feeds provide processed, categorized, and continuously updated threat data to help organizations proactively detect, block, and respond to cyber threats.
Are TreeIQ™ Threat Feeds suitable for OEM and resale?
Yes. Feeds can be customized by category, feed type, delivery method, and update frequency.
Are TreeIQ™ Threat Feeds suitable for OEM and resale?
Yes. They are designed for OEM, white-label, and reseller use.
Is support available for feed integration?
Yes. Integration guidance, API documentation, and onboarding support are provided.
Can Threat Feeds be combined with other TreeIQ™ products?
Access is subscription-based. Contact TreeIQ™ to select feeds and finalize licensing.
